
The attackers knew who they have been going after because it marketed the bogus app as a approach round real-life points with the WalletConnect protocol such because the latter’s included a scarcity of common help for the protocol by broadly used crypto wallets. Since the true WalletConnect open-source protocol didn’t have an official app within the Play Retailer, it will need to have been like taking sweet from a child as greater than 10,000 folks put in the app.
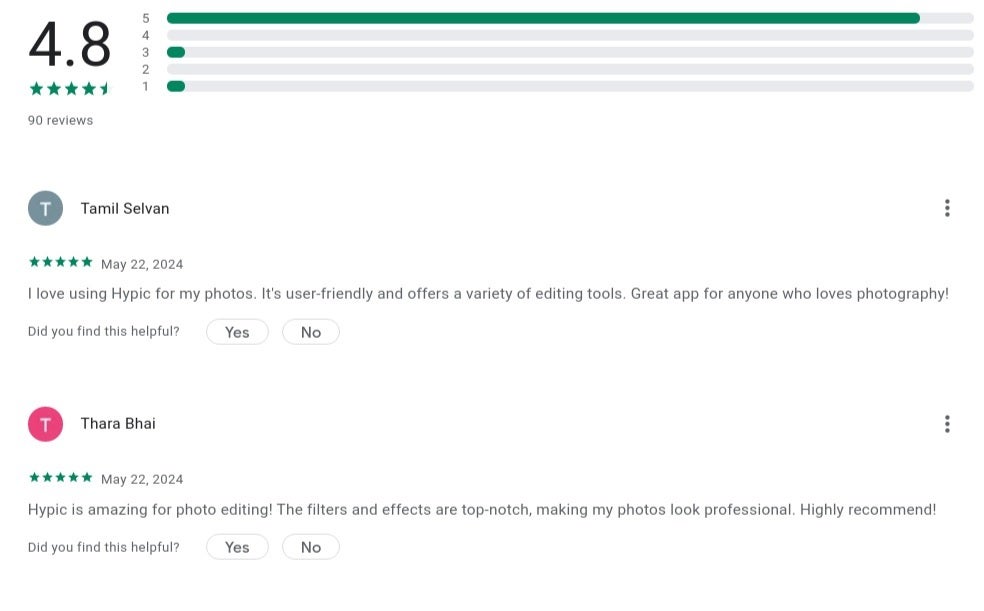
Fke evaluations hiked the ranking of the app and drowned out the destructive evaluations from victims. | Picture credit-Examine Level Analysis
Whereas it was good that the variety of these ripped off by the app was nowhere near the greater than 10,000 Android customers who put in it, CPR found that there have been over 150 addresses linked to verified transactions suggesting that this was the quantity of people that acquired hoodwinked within the rip-off. As soon as the app was put in, a brand new subscriber was prompted to hyperlink his or her cryptocurrency wallets, presumably loaded with cryptocurrency, to the app which customers thought they may belief.
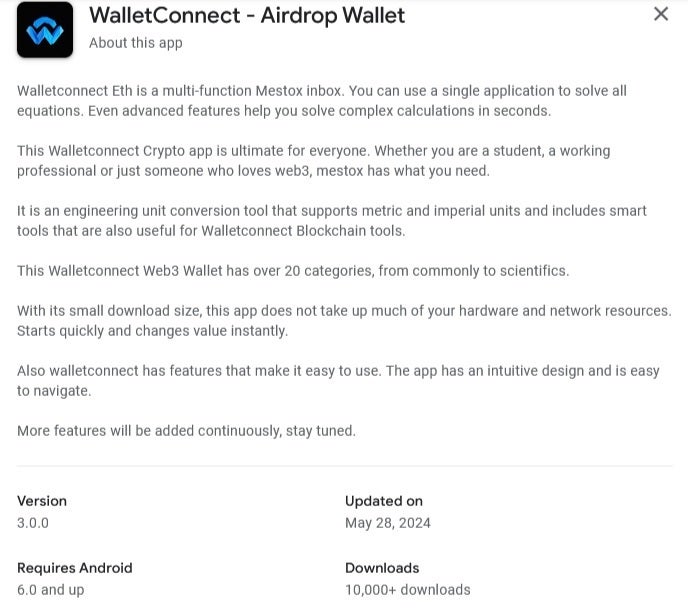
The fraudulent app’s Google Play Retailer itemizing. | Picture credit-Examine Level Analysis
By linking their crypto wallets with the app, customers would expertise safe entry to supported web3 purposes. Web3 is a brand new iteration of the online constructed on blockchain expertise and is managed by the neighborhood of customers. After putting in the app, the customers have been requested to decide on a brand new crypto pockets that supposedly supported the WalletConnect protocol. At this level, the victims have been requested to authorize varied transactions whereas additionally being despatched to a malicious web site.
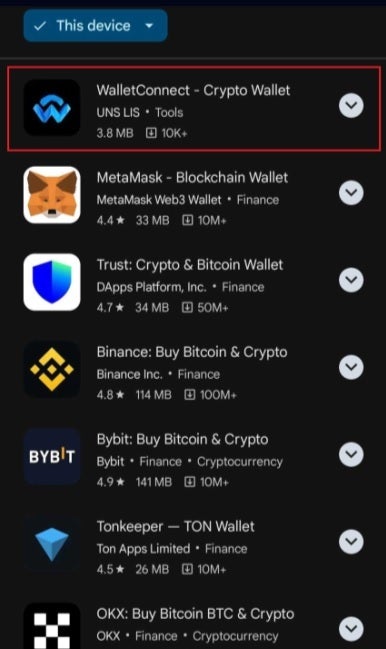
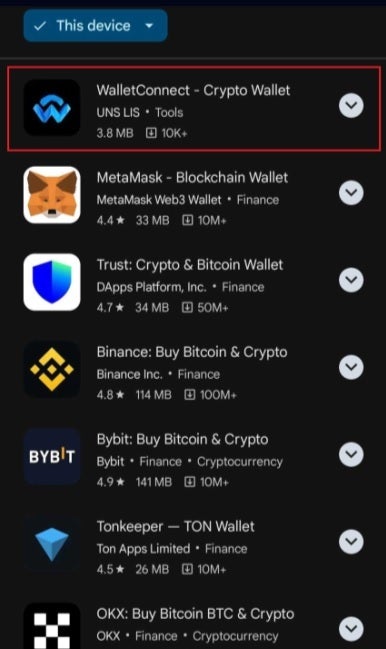
Trying to find WalletConnect in Google Play would deliver up the bogus app on the prime of the record. | Picture credit-Examine Level Analysis
The malicious web site took down all details about the sufferer’s pockets. Utilizing good contracts, the attackers have been capable of switch tokens from the sufferer’s pockets into their very own and even transferred extra worthwhile crypto to themselves over much less worthwhile varieties. Based on CPR, that is the primary time {that a} “crypto drainer” focused cellular gadget customers completely.
“Android customers are robotically protected in opposition to identified variations of this malware by Google Play Defend, which is on by default on Android gadgets with Google Play Companies. Google Play Defend can warn customers or block apps identified to exhibit malicious habits, even when these apps come from sources exterior of Play.”-Google spokesman
Curiously, solely 20 victims determined to write down a destructive evaluation concerning the app within the Play Retailer. This allowed the dangerous actors behind the rip-off to put up tons of constructive evaluations to outnumber the poor evaluations. The app was launched in March however was allowed to look ahead to 5 months earlier than it was faraway from the Play Retailer by Google, however not earlier than $70,000 in crypto was stolen from those that selected to put in WalletConnect from the Play Retailer. In the event you did set up the app, uninstall it instantly.






